Defense in Depth as we all know, multiple layers of security controls placed for protection, did you know about Microsoft EM+S Defense in Depth capabilities?
Microsoft Enterprise Mobility + Security has defensive rings:
-
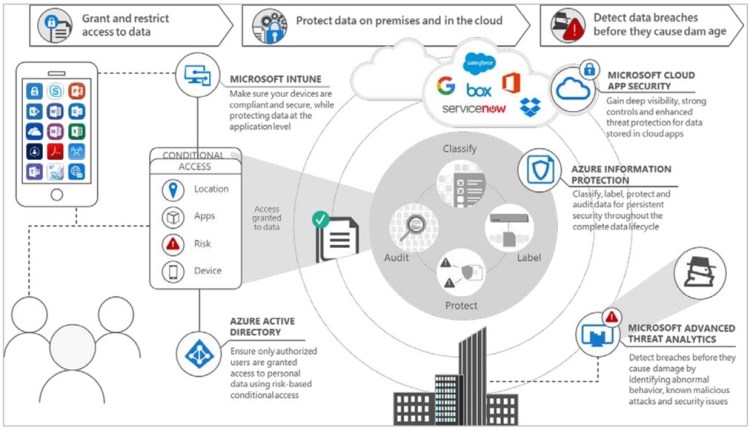
Azure Active Directory (Azure AD) Identity Protection Security Reports, like watchmen in the towers, allow you to see configuration vulnerabilities, which are session and user risk signals that our machine learning, heuristic, and research systems detect.
-
Azure Active Directory Risk-Based Conditional Access,
like guards at the gate, allows you to put those risk signals to work, automatically intercepting bad sign-ins and deactivating compromised passwords. -
Microsoft Cloud Application Security, like a security escort, allows you to monitor and control activity between an app and the user.
-
Advanced Threat Analytics,
like a watchman in the treasury, provides deep forensic insights into what’s happening in your on-premises environment, allowing you to see precisely how a hacker acted in your environment so you can provide a rapid response. -
Azure Active Directory Privileged Identity Management,
like a keeper of keys, ensures that you have the minimum possible administrative attack surface by giving you just-in-time and just-enough administrative access. -
Azure Information Protection,
like guards who protect treasure in transit, allows you to protect data with strong encryption and access policies regardless of where it goes. -
Microsoft Intune Mobile Device Management and Mobile Application Management, like a protector of the armory, help you ensure that devices and apps used in your organization are secure and healthy, again protecting data on these devices against device loss, malware, or other threats.
Putting it together: Defense in Depth and EMS
If you are a Microsoft Partner you should leverage these capabilities and talking points to position EM+S to your O365 customers. I have attached the full document for your reference, this document is old, but it is gold and still relevant to use it today’s scenarios 😊.
Download the document from here – Defense_In_Depth_Enterprise Mobility_and_Security_61517
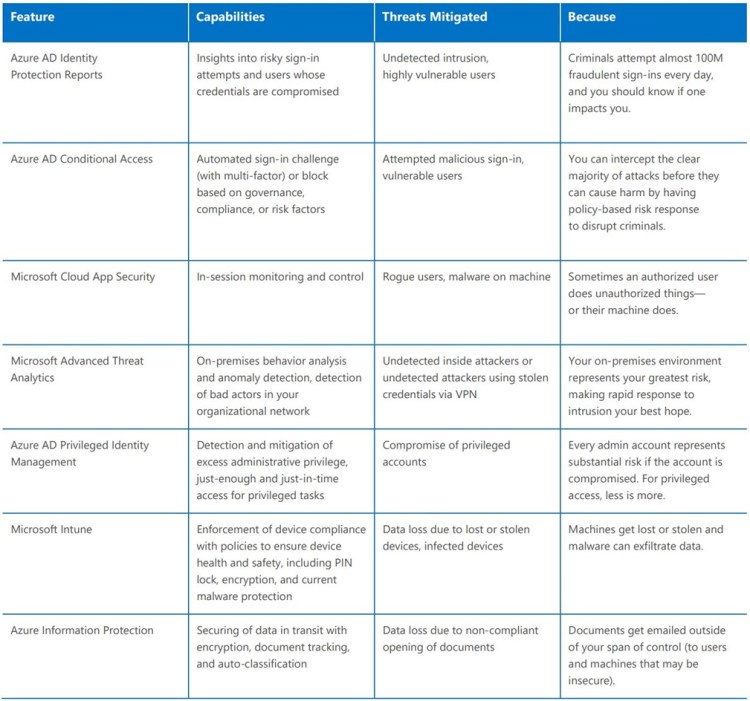
This chart talks about some of the important Features, Capabilities, Threats mitigation.