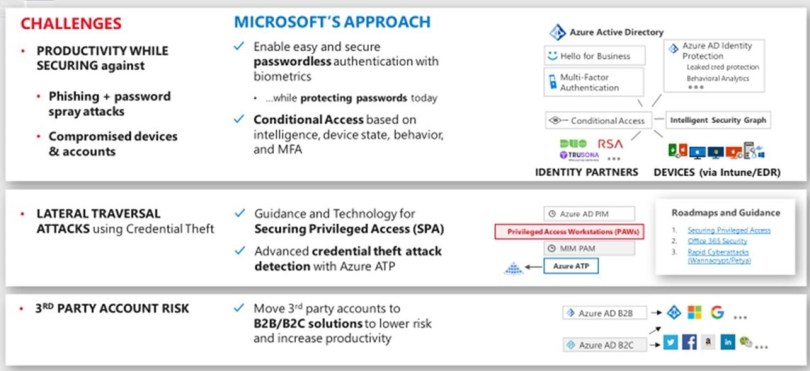
Microsoft is taking a comprehensive approach to securing identities against the full range of threats and risks. Microsoft identity and access management solutions help IT protect access to applications and resources across the corporate data-center and into the cloud. Such protection enables additional levels of validation, such as Multi-Factor Authentication and Conditional Access policies. Monitoring suspicious activity through advanced security reporting, auditing, and alerting helps mitigate potential security issues. Azure Active Directory Premium provides single sign-on (SSO) to thousands of cloud software as a service (SaaS) apps and access to web apps that you run on-premises.
By taking advantage of the security benefits of Azure Active Directory (Azure AD), you can:
- Create and manage a single identity for each user across your hybrid enterprise, keeping users, groups, and devices in sync.
- Provide SSO access to your applications, including thousands of pre-integrated SaaS apps.
- Enable application access security by enforcing rules-based Multi-Factor Authentication for both on-premises and cloud applications.
- Provision secure remote access to on-premises web applications through Azure AD Application Proxy.
Turn on Conditional Access:
Best practice: Manage and control access to corporate resources.
Detail: Configure common Azure AD Conditional Access policies based on a group, location, and application sensitivity for SaaS apps and Azure AD–connected apps.
Enforce multi-factor verification for users:
Best Practice: Enable MFA for all users and login methods with Azure AD Security Defaults Benefit: This option enables you to easily and quickly enforce MFA for all users in your environment with a stringent policy to:
- Challenge administrative accounts and administrative logon mechanisms
- Require MFA challenge via Microsoft Authenticator for all users
- Restrict legacy authentication protocols.
This method is available to all licensing tiers but is not able to be mixed with existing Conditional Access policies. You can find more information in Azure AD Security Defaults
Enable Multi-Factor Authentication with Conditional Access policy:
Benefit: This option allows you to prompt for two-step verification under specific conditions by using Conditional Access. Specific conditions can be user sign-in from different locations, untrusted devices, or applications that you consider risky. Defining specific conditions where you require two-step verification enables you to avoid constant prompting for your users, which can be an unpleasant user experience.
Enable Multi-Factor Authentication with Conditional Access policies by evaluating Risk-based Conditional Access policies.
Benefit: This option enables you to:
- Detect potential vulnerabilities that affect your organization’s identities.
- Configure automated responses to detected suspicious actions that are related to your organization’s identities.
- Investigate suspicious incidents and take appropriate action to resolve them.
Actively monitor for suspicious activities:
An active identity monitoring system can quickly detect suspicious behavior and trigger an alert for further investigation.
Best practice: Have a method to identify:
- Attempts to sign in without being traced.
- Brute force attacks against a particular account.
- Attempts to sign in from multiple locations.
- Sign-ins from infected devices.
- Suspicious IP addresses.
Detail: Use Azure AD Premium anomaly reports. Have processes and procedures in place for IT admins to run these reports on a daily basis or on demand (usually in an incident response scenario).
Azure ATP (Advanced Threat Protection):
Azure Advanced Threat Protection (ATP) is a cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization.
Azure ATP enables SecOp analysts and security professionals struggling to detect advanced attacks in hybrid environments to:
- Monitor users, entity behavior, and activities with learning-based analytics
- Protect user identities and credentials stored in Active Directory
- Identify and investigate suspicious user activities and advanced attacks throughout the kill chain
-
Provide clear incident information on a simple timeline for fast triage
Azure AD Privileged Identity Management:
Privileged Identity Management provides time-based and approval-based role activation to mitigate the risks of excessive, unnecessary, or misused access permissions on resources that you care about. Here are some of the key features of Privileged Identity Management:
- Provide just-in-time privileged access to Azure AD and Azure resources
- Assign time-bound access to resources using start and end dates
- Require approval to activate privileged roles
- Enforce multi-factor authentication to activate any role
- Use justification to understand why users activate
- Get notifications when privileged roles are activated
- Conduct access reviews to ensure users still need roles
- Download audit history for internal or external audit
For more information and best practices you can refer to this link – https://docs.microsoft.com/en-us/azure/security/fundamentals/identity-management-best-practices