To be successful with threat intelligence, you must have a large diverse set of data and you have to apply it to your processes and tools. Microsoft has done both and this is how we apply it.
The data that we collect from the various sources passes through a strict privacy/compliance boundary to ensure that data is only being used in ways that our customers have agreed to. Microsoft takes this responsibility very seriously.
NOTE: Data from dark (criminal) markets is one part of the (much) larger scope of intelligence that we integrate into our products and services.
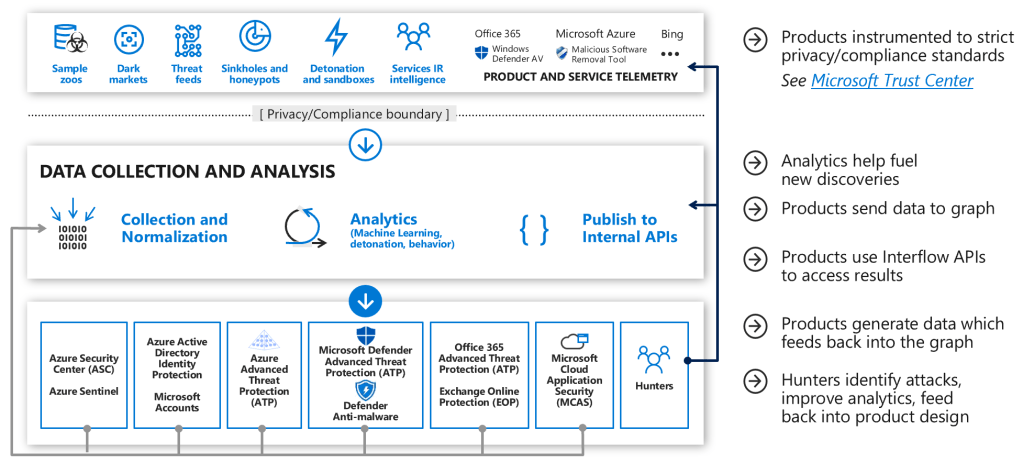
Data Collection and Analysis – The data then goes through a collection and analysis phase to normalize it, apply various analytics (listed) to identify relevant security insights and findings, and publish to an internal API
Products – Each of the products then access the data to provide findings, context, insight, etc. relative to that capability and then automatically feed new insights back into the graph to enrich other product findings.
Hunters – Additionally, human teams are constantly working with the graph to hunt for adversaries in various environments (Azure, Office 365, Microsoft IT, Windows ATP Customers, etc.) as well as creating, tuning, and validating new analytics to improve the detection overall.
Some more additional information:
1. Microsoft has over 4 Trillion files in our malware sample zoo.
2. Microsoft collects over 8 million indicators of compromise each day.
3. We also use external threat feeds to enrich and validate our findings.
4. We directly include intelligence from onsite investigations into attacks into the graph.
And with all those services and data, we have a tremendous amount of surface area that we defend. On any given day, we see more attacks than most other companies, and we gain a lot of information from defending against those attacks.