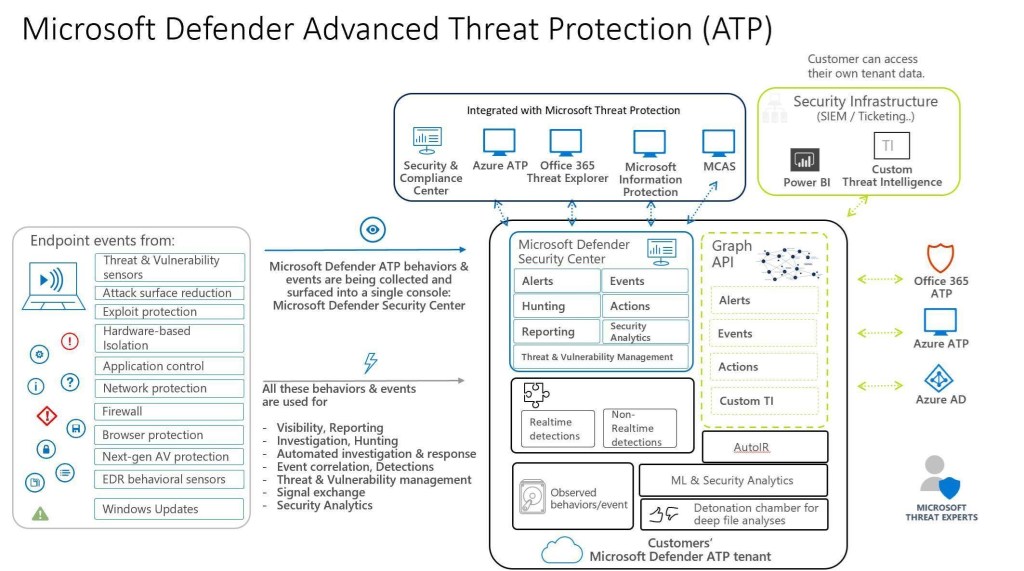
Every customer has their own Microsoft Defender ATP tenant in the cloud, separated from other customers.
All Microsoft Defender ATP behaviors & security events are collected and sent to the customer tenant.
Those events are being used for:
- Visibility, and Reporting
- Investigation, and threat hunting
- Automated investigation & response
- Event correlation, and detections
- Prioritized Threat & Vulnerability management
- Signal exchange with other Microsoft Threat Protection services
Each tenant comes with
- A single console for Security Operations: the Microsoft Defender Security Center
- A new management dashboard for Security Admins: The M365 Security and Compliance Center
- Reports
- Comprehensive toolset for SecOps
- A rich behavioral IOAs dictionary
- A sandbox environment for deep file analysis
We provide rich APIs to allow customers integrate with their existing security solutions, such as SIEM, Ticketing systems, upload their own custom TI, or other partner solutions.
Our managed threat hunting service, Microsoft Threat Experts, monitors and hunts over de-identified data.
Microsoft Defender ATP offers out of the box integration with Azure AD, Azure ATP, Azure Security Center, Azure Information Protection, Microsoft Cloud App Security, Microsoft Intune, and Office 365 ATP.
Hi Kiran, is this diagram available in a PowerPoint or similar somewhere? We’d love to add it to the regular deck. Regards, Dave C
LikeLike
Hi Dave, I don’t have the Powerpoint version, but you can download the PDF from the same article from my blog post. Let me know if you want me to send over email to you as well.
LikeLike