A step by step information for preparing a successful Microsoft Defender ATP POC.
Trial Information
- Trials are good for 60 days.
- Trials can convert to production without issue. We encourage linking a trial to a production Azure AD instance so once purchased the trial becomes production. This also helps when with trialing Office ATP or if it is already owned as the linking of the services can be done with a simple check mark.
- If you already have MDATP licenses (either as E5 or otherwise), you can already start setting up the MDATP service and console now. More information on the MDATP documentation.
Things You Need to get Started
- Access to Azure AD Global Admin
- Firewall/Proxy set up – Configure endpoint proxy and Internet connectivity settings
Operating Systems to test
- A Windows 10 Enterprise version 1809 machine
- An additional Windows 10 Enterprise version 1607 or later machine
- A Windows 7 SP1 Enterprise (if needed)
- A Windows 2012 R2 Server, Windows 2016 Server, and/or Windows 2019 Server machine
- A Linux client
- A Mac client
Sign up for Trial
- After the EULA is signed, the request will be sent to the MDATP Product. This typically takes between 12 to 24 hours. If you need to expedite due to an urgent need, contact your friendly Microsoft PTS or me for assistance.
- Once approved, the email used to sign up for trial will receive an email:

- Click “Activate your trial now”:
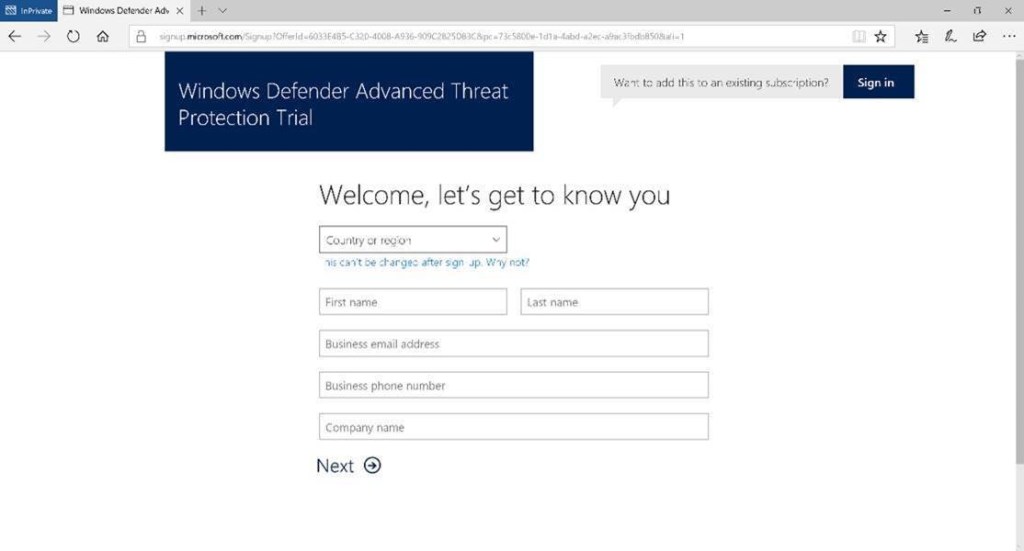
- If you already have an Azure AD instance do not fill this out. If you do, it will spin up a new AAD instance. If there is an existing AAD instance, click the “Sign In” button in the upper right. Sign in with an account that has the “Global Admin” role in Azure AD. This is required to set up the instance but not for day to day administration.
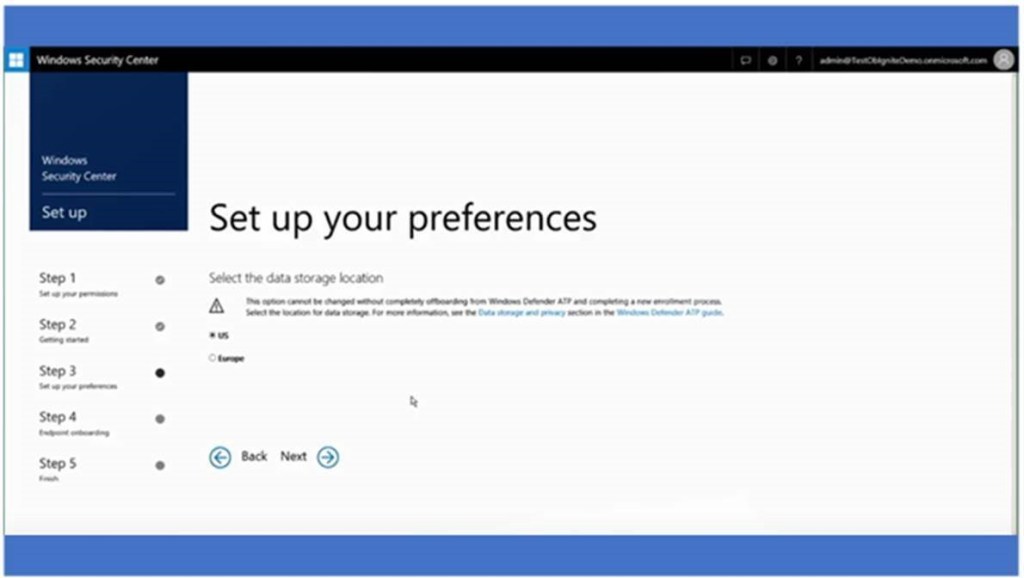
- After logging in, the following screen appears:

- Pick the location that meets the company’s needs. Data can only reside in one location and this cannot be changed. It is not possible to move an instance from one location to another without a total offboard, wipe, onboard, with all data being lost.
- This section is to help size the MDATP cloud instance. Mainly for engineering use.

- This is for informational purposes.

- Once set up is completed, there will be a prompt to onboard machines. This can be done via Group Policy, SCCM, Intune/MDM or by a script. The script will only onboard ten machines. Instructions for Onboarding are listed below.
Configure endpoints using Group Policy
Configure endpoints using System Center Configuration Manager
Configure endpoints using Mobile Device Management tools
Configure endpoints using a local script
Configure non-persistent virtual desktop infrastructure (VDI) machines
- Confirm that machine has been onboarded successfully
- Open an elevated command-line prompt on the endpoint and run the script: powershell.exe -NoExit -ExecutionPolicy Bypass -WindowStyle Hidden (New-Object System.Net.WebClient).DownloadFile(‘http://127.0.0.1/1.exe’, ‘C:\test-WDATP-test\invoice.exe’);Start-Process ‘C:\test-WDATP-test\invoice.exe’
- Check the Event Logs
- Windows Logs > Application with Event Source WDATPOnboarding and Event ID 20
Testing
Upon completion of setup, a Setup, Walkthrough, and Attack DIY document will be sent. The scenario is a “malicious” phishing attack. The payload is not malicious but will appear so in the console so you can track an attack.
If you would like to run additional attack scenarios, there are tutorials to 5 different simulations you can run, found in the Help (?) icon on the top right. They include walkthroughs and matching simulation files. The scenarios you can test are:
- Document drops backdoor
- PowerShell script in fileless attack
- Automated Investigation (backdoor)
- Automated Investigation (fileless attack)
- Custom Detections
Additional Tests to perform (current)
- Stop and Quarantine a file
- Remove file from Quarantine
- Block a file
- Remove file from blocked list
- Isolate a machine
- Undo machine isolation
- Collect an investigation package
- Run Windows Defender Antivirus scan
- Restrict applications from running
- Undo restriction of application from running
- Use search feature
- Onboard a server
- Set up machine groups and tags
- Power BI reporting
- Setup Secure Score
- SIEM Integration
- Understand and Review an Automatic Investigation
- Advanced Hunting
Keys to Success
- Do not disable Windows Defender AV via policy or some other way (registry, disable service, etc.) It does not need to be the primary AV but the service must be enabled.
- How to Ensure that Windows Defender Antivirus is not disabled by a policy
- If you’re running a third-party antimalware client and use Mobile Device Management solutions or System Center Configuration Manager (current branch) version 1606, you’ll need to ensure that the Windows Defender Antivirus ELAM driver is enabled.
- Clients must be Windows 10 Anniversary (1607) or higher
- Check proxy configuration. Use the connectivity verification tool to confirm endpoint communication is working.
- If using authenticated proxy, exclude Microsoft URLs. Remember this is WinHTTP proxy so settings in IE/Chrome/Edge don’t matter. You must set WinHTTP. Proxy documentation is located here.
- The more machines onboarded the better the results.