This is a helpful document on the M365 information protection and compliance deployment acceleration guide. Use this acceleration guide to learn best practices and key benefits of using Microsoft Information Protection & Compliance, and how you can get the most out of your customer Microsoft 365 investments.
Download the document here – Microsoft Information Protection and Compliance Deployment Acceleration Guide_5-18-2020 (1)
Microsoft is in a unique position to help you with more intelligent compliance and risk management solutions. First, we understand ‘compliance’ can have different meanings to various teams across the enterprise. Compliance is an outcome of continuous risk management, involving compliance, risk, legal, privacy, security, IT, HR, and finance teams which requires an integrated approach to manage risk Let’s start with the base pillar, Compliance Management: compliance management is all about simplifying risk assessment and mitigation in a more automated way, providing visibility and insights to help meet compliance requirements.
Information Protection and Governance: we believe there is a huge opportunity for Microsoft to help our customers know their data better, protecting and governing data throughout its life cycle in a heterogeneous environment. This is often the key starting point for many of our customers in their modern compliance journey – knowing what sensitive data they have, creating flexible, end-user friendly policies for both security and compliance outcomes and using more automation and intelligence.
Internal Risk Management: Internal risks are often what keeps business leaders up at night – regardless of whether negligent or malicious, identifying and being able to take action on internal risks are critical. The ability to quickly identify and manage risks from insiders (employees or contractors with corporate access) and minimize the negative impact on corporate compliance, competitive business position and brand reputation is a priority for organizations worldwide.
Last but not least, Discover and Respond: being able to discover relevant data for internal investigations, litigation, or regulatory requests and respond to them efficiently, and doing so without having to use multiple solutions and moving data in and out of systems to increase risk – is critical. The life cycle of a specific document will be comprised of the following phases: Discover, Classify, Protect, and Monitor. During each of these steps, the document will become incrementally better managed and more secure.
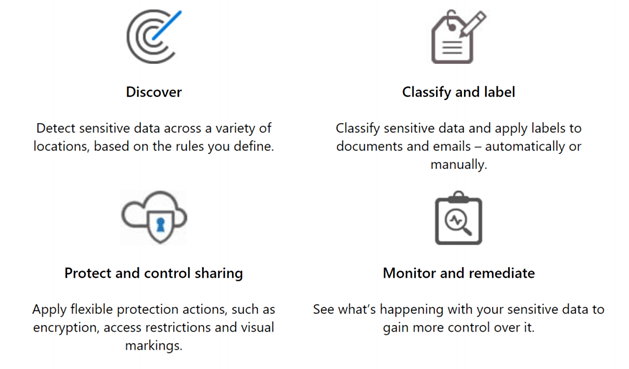
Interestingly, deployment of this technology will also include these four phases, since experience shows it is best to introduce each of these capabilities in orderly succession. At each step, your information becomes better managed and more secure, and you don’t need to wait until you are ready to go all the way to begin realizing value from your investments.