Have you ever been wondered how to deploy step by step for Microsoft 365 Threat Protection suite?

Microsoft 365 E5 enables you to protect your organization with adaptive, built-in intelligence. With the threat protection features in Microsoft 365 E5, you can detect and investigate advanced threats, compromised identities, and malicious actions across your on-premises and cloud environments.
In Microsoft 365 E5, threat protection capabilities are integrated by default. Signals from each capability add strength to the overall ability to detect and respond to threats. The combined set of capabilities offers the best protection for organizations, especially multi-national organizations, compared to running non-Microsoft products. As soon as you deploy any of the advanced threat protection capabilities, you can turn on Microsoft Threat Protection, which brings the signals and data together into one place.
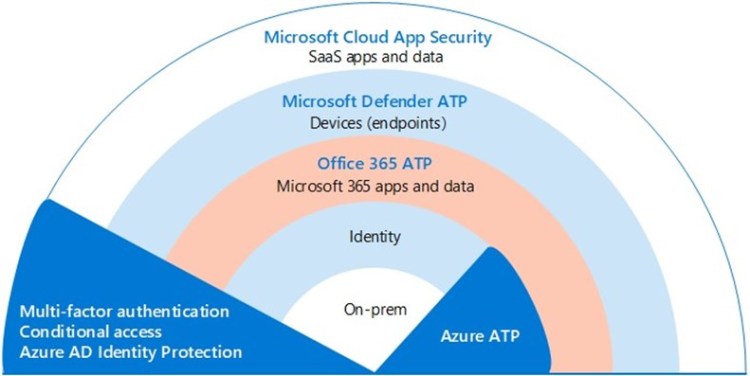
The below image illustrates a recommended path for deploying these individual capabilities.
| Solution/capabilities | Description | |
| Step 1 | Multi-factor authentication and conditional access
|
Protect against compromised identities and devices. Begin with this protection because it’s foundational. The configuration recommended in this guidance includes Azure AD Identity Protection as a prerequisite. |
| Step 2 | Azure Advanced Threat Protection | A cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization. Focus on this next because it protects your on-prem and your cloud infrastructure, has no dependencies or prerequisites, and can provide immediate benefit. |
| Step 3 | Office 365 Advanced Threat Protection | Safeguards your organization against malicious threats posed by email messages, links (URLs), and collaboration tools. Protections for malware, phishing, spoofing, and other attack types. This is recommended next because change control, migrating settings from incumbent system, and other considerations can take longer to deploy.
Note: Be sure you also configure the threat protection capabilities included in all Office 365 subscriptions (Exchange Online Protection). |
| Step 4 | Microsoft Defender Advanced Threat Protection | An endpoint protection platform that helps prevent, detect, investigate, and respond to advanced threats. This takes longer to deploy, but can be done in parallel with the other capabilities if other admins are responsible. |
| Step 5 | Microsoft Cloud App Security | A cloud access security broker for discovery, investigation, and governance. You can enable this early to begin collecting data and insights. Implementing information and other targeted protection across your SaaS apps involves planning and can take more time. |
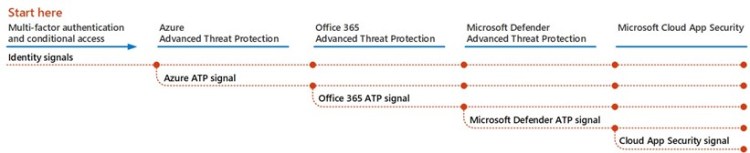
Your threat protection features can be configured in parallel, so if you have multiple security teams responsible for different services, they can configure your organization’s protection features at the same time.
The following diagram illustrates the high-level process for deploying threat protection capabilities.
