I am sure most of you might have heard about Fileless threat? What exactly are fileless threats? The term “fileless” suggests that a threat does not come in a file, such as a backdoor that lives only in the memory of a machine. However, there’s no generally accepted definition for fileless malware. The term is used broadly; it’s also used to describe malware families that do rely on files to operate.
The switch from application-based malware (PE) being the dominate form to fileless has been like a tsunami. The total volume of malware has grown 300% per year over the last 5 and we’ve seen fileless become the top form factor. Let’s take a more technical look at fileless attacks and how that work. While there is no widely accepted definition for a fileless attack it’s generally one where the attack isn’t conducted completely within a malicious app that the attacker manages persist as executable files on the device. What often defines what fileless attack is, is how it persists itself over time. Often the malicious code that the attack runs are hidden within something else, like document, or WMI, or even the registry. Sometimes it may persist as files on disk, but they won’t be a typical executable file.
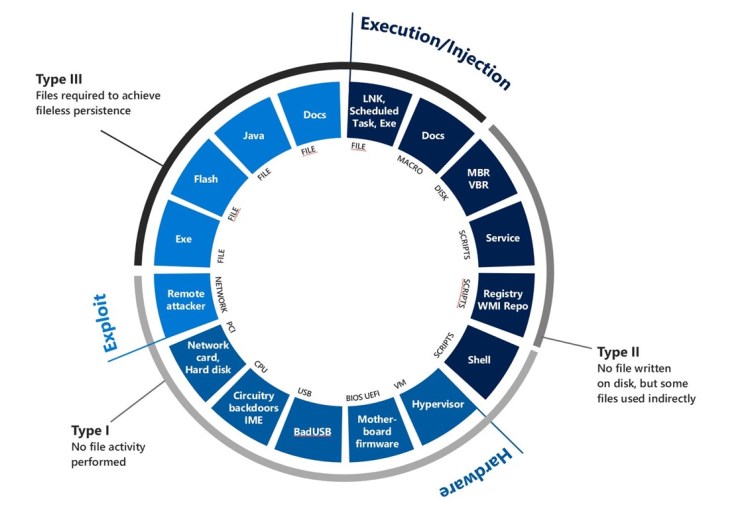
There is a wide range of approaches to fileless attacks and we’ve classified them by their entry point. (i.e., execution, injection, exploit, hardware) and then form type of entry point.
For the Execution entry point the malicious attack requires the execution of something like a shortcut, scheduled tasks, or code, like a macro, embedded inside of something like a document. In this case it’s the execution of the shortcut, task, or macro code within a document that enables the attack to start.
For the Injection entry point the attacker injects their malicious code inside of a repository like the registry, WMI.
For the Hardware entry point the attacker will tamper with the device or use malicious hardware, like a USB drive with malicious firmware, to compromise a target device.
For the Exploit entry point these types of attacks may come in the form of a remote attack where malicious network packets are used to exploit a vulnerability on the receiving service. The same type of attack could be used to compromise an app like a browser while a user visits a site that has been setup to serve malicious code in the interest of compromising the browser.
Fileless attacks may or may not use any files to conduct an attack and can be classified as follows:
- Type I – No files are required on the device. A malicious USB device or backdoors built into the hardware of the device itself are good examples.
- Type II – No files are written on disk, but some files may be used indirectly. In this case the attack doesn’t persist its own self-created files and instead it may indirectly store malicious content in the registry or WMI which is stored as a file on the disk
-
Type III – In this case the attack uses a file as a mean to initiate attack but one done it the malicious code that is persists and necessary to perpetuate the attack goes completely fileless.
Microsoft Defender ATP’s antivirus capabilities are designed to detect attacks that come through any of these entry points using a machine learning and a deep library of behaviors-based Indicators of Attack (IOA). Through AntiMalware Scan Interface (AMSI), behavior monitoring, memory scanning, and boot sector protection, Microsoft Defender Advanced Threat Protection can inspect fileless threats even with heavy obfuscation. Machine learning technologies in the cloud allow us to scale these protections against new and emerging threats.