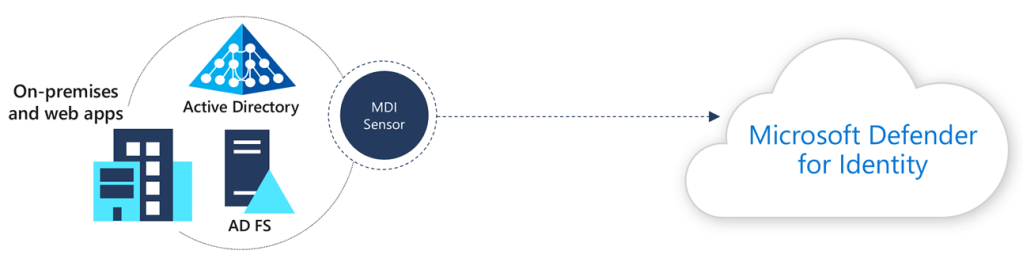
Microsoft Defender for Identity (formerly Azure Advanced Threat Protection, also known as Azure ATP) is a cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization.
Defender for Identity enables SecOp analysts and security professionals struggling to detect advanced attacks in hybrid environments to:
- Monitor users, entity behavior, and activities with learning-based analytics.
- Protect user identities and credentials stored in Active Directory.
- Identify and investigate suspicious user activities and advanced attacks throughout the kill chain.
- Provide clear incident information on a simple timeline for fast triage.
Microsoft has recently released some new capabilities in Defender for Identity, so lets learn what it is:
New Sensor installation options: Active Directory Federation Services (AD FS) servers Defender for Identity now supports installing sensors on Active Directory Federation Services (AD FS) servers. Installing the sensor on compatible AD FS Servers extends Microsoft Defender for Identity visibility into hybrid environments by monitoring this critical infrastructure component. We also refreshed some of our existing detections (Suspicious service creation, Suspected Brute Force attack (LDAP), Account enumeration reconnaissance) to work on AD FS data as well. To start deployment of the Microsoft Defender for Identity sensor for AD FS servers, download the latest deployment package from the sensor configuration page.
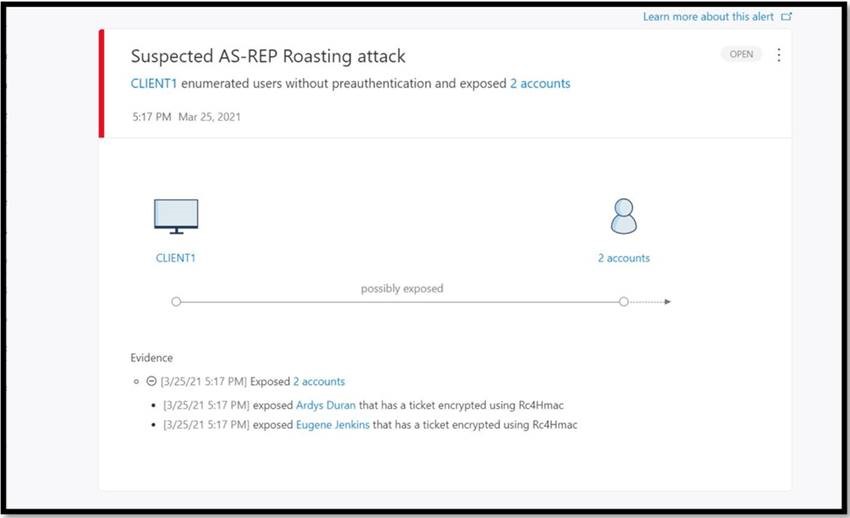
New security alert: Suspected AS-REP Roasting attack: Defender for Identity’s Suspected AS-REP Roasting attack security alert is now available. In this detection, a Defender for Identity security alert is triggered when an attacker targets accounts with disabled Kerberos pre-authentication, and attempts to obtain Kerberos TGT data. The attacker’s intent may be to extract the credentials from the data using offline password cracking attacks. For more information, see Kerberos AS-REP Roasting exposure.
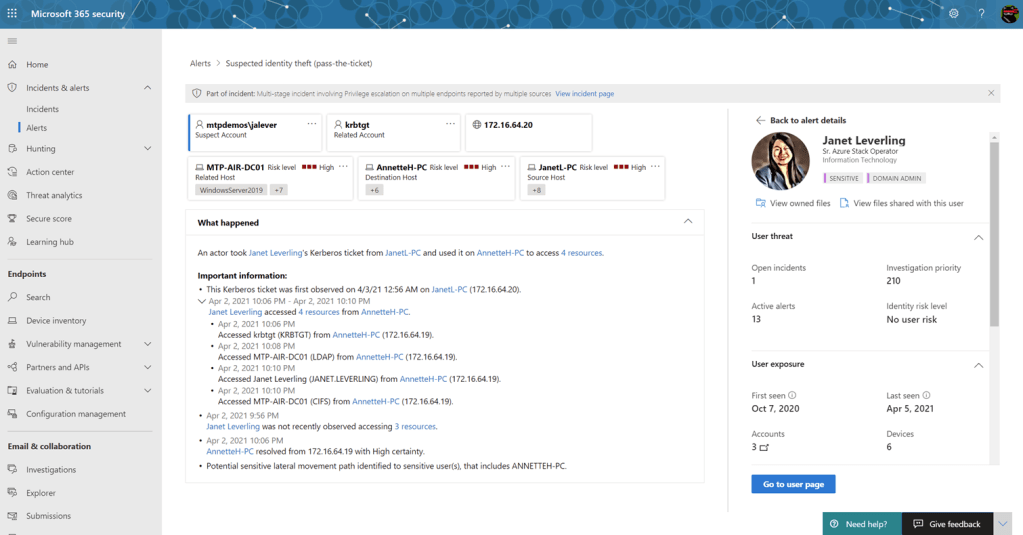
New feature in public preview: MDI Alert page
With this new capability, SecOps can now view MDI alerts natively in the new M365 security portal: security.microsoft.com
Also making its first appearance is our new User side pane.
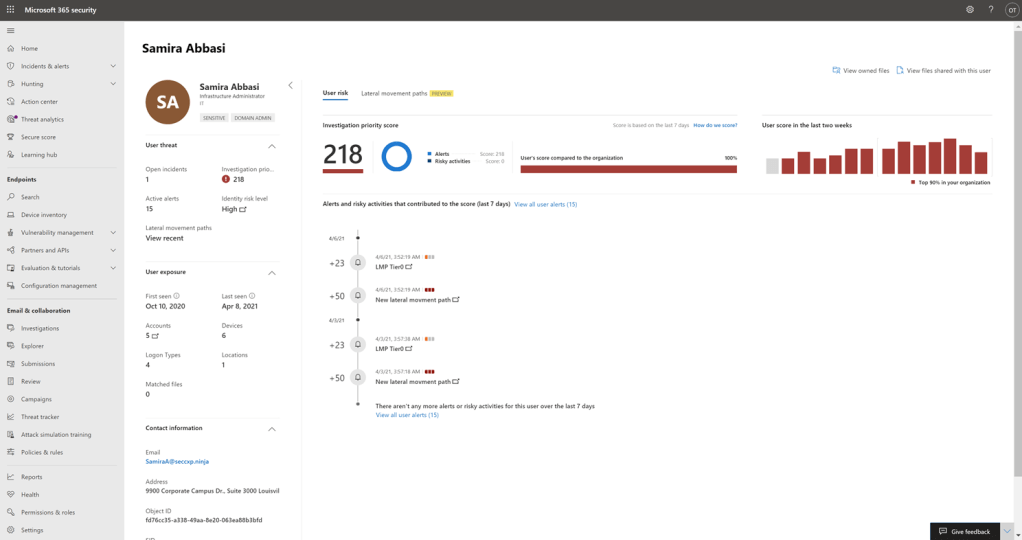
New feature in public preview: MDI User page Also making its way to the new portal is the unified User page. It covers not only what you’ve come to expect out of the existing MDI user page in the Cloud App Security portal, but is now enhanced with additional M365 workloads and without the need to jump between portals.
New monitored activity: Computer Account Created
Microsoft Defender for Identity now correlate Windows 4741 events into the “Computer account added” activity, To take advantage of this, make sure that your auditing policy is configured properly.
Updated security alert: Suspected Kerberos SPN exposure
Based on customer feedback, Microsoft updated the severity for the Suspected Kerberos SPN exposure to high to better reflect the impact of the alert. For more information about the alert, see Suspected Kerberos SPN exposure
Updated security alert: Active Directory attributes reconnaissance (LDAP).
We’ve improved our Active Directory attributes reconnaissance (LDAP) alert to also detect techniques used to obtain the information needed in order to generate security tokens, such as those as part of the Solorigate campaign.
Updated security alert: Suspected Netlogon privilege elevation attempt.
Our Netlogon detector alert has been enhanced to also work when the Netlogon channel transaction occurs over an encrypted channel. For more information about the detector, see Suspected Netlogon privilege elevation attempt or read this blog.
New Video: This cool new video about one of the most popular pillar of Microsoft Defender for Identity, its security posture assessments. Defender for Identity Video in YouTube.
New Microsoft Defender for Identity Ninja training: Want to become an MDI Ninja and get this cool certificate? Than complete this new training, part of the M365 Ninja series.
