The amount of data in organizations is ballooning at 50 percent year over year. According to the some Data Breach Investigations Report, Ransomware attacks rose by 92.7% in 2021 compared to 2020 levels, with 1,389 reported attacks in 2020 and 2,690 in 2021. Microsoft Security Intelligence Report has extensive Microsoft research on software vulnerabilities, vulnerability exploits, and threats like malware. Many organizations don’t have threat managers, threat analysts, or a threat intelligence framework. Microsoft has infused threat intelligence into our products and services.
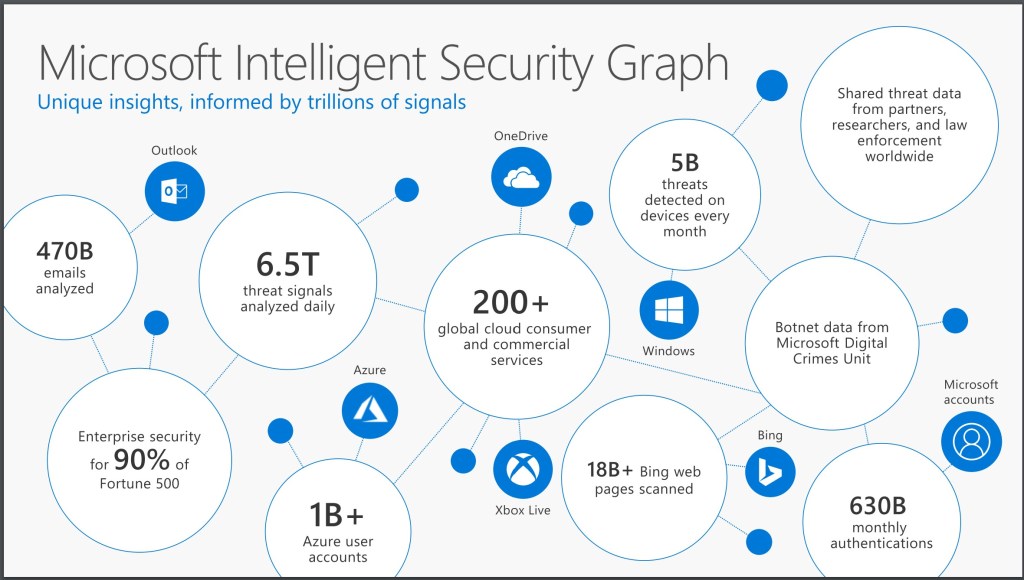
With the right context, this intelligence leads to targeted actions such as system updates or enforcing security policies like multi-factor authentication, or apply other security measures. Threat intelligence is built into Microsoft products and services to give context, relevance, and priority to help people take action against cyberthreats. Threat intelligence producers at Microsoft provide relevance and tell why something’s bad, which is just the type of information security analysts want. Microsoft’s Intelligent Security Graph is foundational for embedding security in Office 365, M365, Azure, Windows, and other products. The Microsoft Threat Intelligence Center (MSTIC) team collects the threat intelligence that’s infused into products and services.
MSTIC aggregates data from sources such as honeypots, malicious IP addresses, botnets, malware detonation feeds. With Microsoft Threat Intelligence, we’ve empowered our customers to have their own threat intelligence on the cyberthreat landscape. It gives insights on advanced threats, malware, phishing, and other attacks for proactive defense. The threat dashboard, Threat explorer, incidents, and alerts are available in the https://security.microsoft.com . Microsoft has built a vast repository of threat intelligence data in M365 Defender.
Organizations can see threat families over time, top threats, and top targeted users. Threat explorer lets you drill down into the history of a threat to see each attachment with a specific malware threat. In the M365 Security and Compliance Center, you can remediate emails in real time. Use filters to find the email you want to investigate and then create an incident. The Management Activity API gives visibility into user, admin, system, and policy actions and events.
Microsoft uses technologies in the M365 security stack such as: Defender for Office365, Exchange Online Protection in Office 365 Threat Intelligence. These tools help organizations proactively defend against advanced threats, malware, phishing, zero-day attacks, and other attacks. Email that contains unsafe attachments and links can carry many advanced threats like zero-day attacks and advanced phishing campaigns. Microsoft uses Defender for Office365 suite to proactively defend against these threats. Microsoft’s Threat explorer tool has transformed how Microsoft detects, investigates, and responds to email threats.
Malicious emails left in user mailboxes are like ticking time bombs. The faster those emails can be removed or purged, the better. Now, security analysts can take direct action against emails to rapidly contain threats. The threat protection capabilities in M365 Defender solutions and Threat Intelligence help to identify, investigate, and respond to attacks better than ever before.
Integrations with Defender for Endpoint and Threat explorer allow Security analysts to rapidly and precisely target email threats. Microsoft is constantly enhancing the ability to identify, prioritize, and respond to the biggest threats to the company. For M365 Threat Intelligence our roadmap includes new capabilities such as add-on block-list capabilities and more proactive understanding of the threat landscape. Microsoft has built a security and threat intelligence framework based on billions of signals that it gathers. Threat intelligence is infused into products and services.