The MITRE Center for Threat-Informed Defense, Microsoft, and other industry partners collaborated on a project that created a repeatable methodology for developing a top MITRE ATT&CK® techniques list.
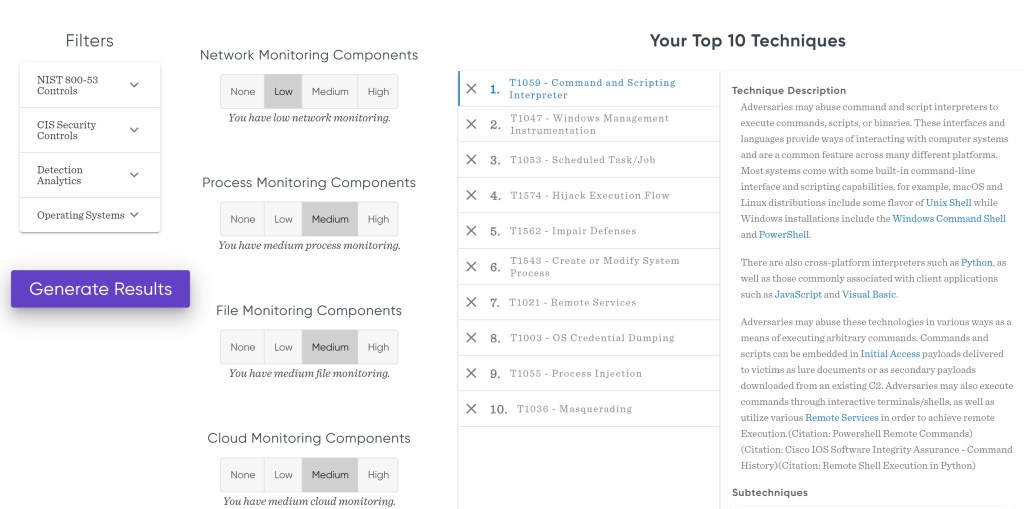
The project also included the development of a customizable, web-based calculator that seeks to prioritize techniques based on a defender’s input, making the methodology even easier to apply to different environments and scenarios. With this calculator, an organization can create a tailored technique list based on various aspects like the maturity of their security operations and the tools that they use.
Practical applications and future work the methodology and insights from the top techniques list has many practical applications, including helping prioritize activities during triage.
Link to access the calculator – https://top-attack-techniques.mitre-engenuity.org/calculator
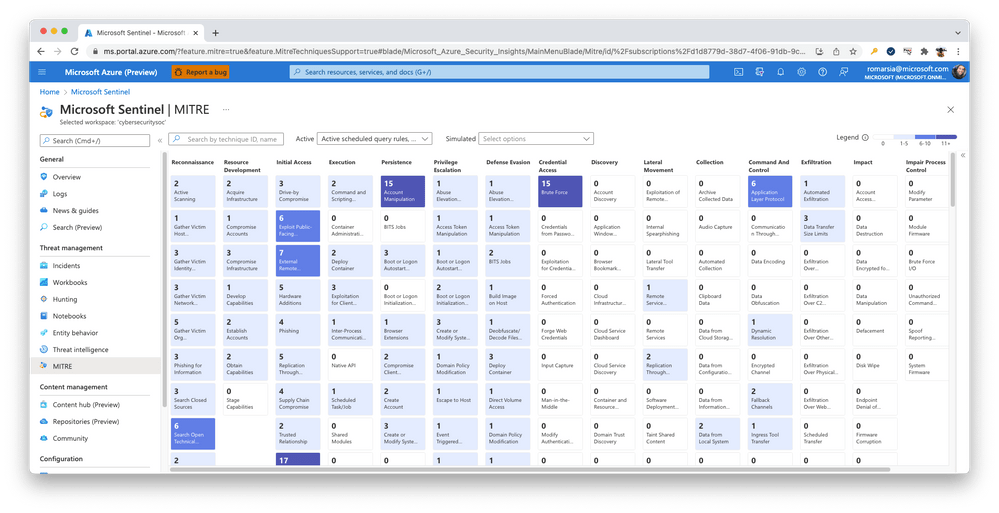
Through products like Microsoft 365 Defender and Microsoft Sentinel, Microsoft is able to better safeguard its customers thanks to insights from industry-wide partnerships like this one. Microsoft processes trillions of signals every day, and our professional monitoring of the threat landscape further informs these solutions. For instance, by utilizing a Zero Trust approach to reduce the attack surface and the likelihood that ransomware attacks will be successful, we can deliver cross-domain defense against human-operated ransomware. This is made possible by our thorough understanding of and research into the ransomware ecosystem.
In the recent MITRE Engenuity ATT&CK® 2022 Evaluations, Microsoft demonstrated complete visibility and analytics on all stages of the attack chain, with 100% protection coverage, blocking all stages in early steps (pre-ransomware phase), including techniques within the top 10 ransomware techniques list that were tested.
For more details please visit this Official Microsoft blog post – https://www.microsoft.com/security/blog/2022/05/11/center-for-threat-informed-defense-microsoft-and-industry-partners-streamline-mitre-attck-matrix-evaluation-for-defenders/