Using multiple cloud platforms can create inconsistent infrastructures that don’t scale across environments. This can lead to increased complexity, additional costs, network security gaps, and risks to business-critical applications and data. Microsoft Purview can help unify security, compliance, and data protection across your enterprise. More than 40 percent of corporate data is dark, meaning it’s not classified, protected, or governed. Every organization needs to be able to securely share data both internally and with partners and customers.
Consider a multi-cloud data protection and security solution that:
Unifies automatic data discovery and data protection. Your multi-cloud data-protection solution should provide complete security and compliance features that cover both first- and third-party apps and services, including Personally Identifiable Information (PII) such as home addresses, dates of birth, and Social Security numbers. Look for features such as built-in sensitivity labeling within applications and services, as well as pop-up user notifications that assist in educating users on best security practices. These features ensure that all sensitive data is correctly categorized and tagged, preventing unauthorized file exfiltration.
A data-protection solution that includes rights management, automated encryption of emails (and attachments), and co-authoring of encrypted documents would aid in ensuring secure cooperation. Your multi-cloud security tool should be adaptable enough to permit manual labeling of some sensitive files for leadership-only access (such as mergers and acquisitions projects), while also allowing administrators to automatically label and protect business files stored in Microsoft SharePoint or Microsoft Teams (like Confidential labels for Finance or HR records). This tool should be capable of scanning and classifying both on-premises file sharing and cloud applications and services.
Prevents the exfiltration of sensitive files and documents to third-party applications and services. More than forty percent of business data is unstructured. It is not classified, protected, or regulated. This invites danger in the form of sensitive data leakage, which can hurt your reputation and, in the instance of disclosed personally identifiable information (PII), result in an expensive lawsuit. Your multi-cloud security solution should be able to classify files and documents, apply sensitivity labels, offer sharing controls and file governance, and implement near real-time data loss prevention policies to prevent data leakage across third-party applications.
Utilizes data discovery automation across structured and unstructured data. Every firm must be able to share data internally and with partners and customers in a secure manner. Your data protection solution must therefore provide data scanning and categorization for all asset types across multi-cloud and on-premises settings. A comprehensive map of your data estate should include metadata and descriptions of data assets. On top of this map, purpose-built applications can generate settings for data discovery, access management, and data landscape insights.
Applies Zero Trust principles to your whole digital enterprise. This includes implementing strong multifactor authentication to validate user identities and maintaining compliance across all endpoints. In addition to incorporating governance and compliance regulations, your data-protection solution should integrate continuous risk assessment and forensics capabilities. Classifying, tagging, and encrypting emails and documents, as well as providing adaptive access to the software as a service (SaaS) applications and on-premises applications, should be additional essential functions.
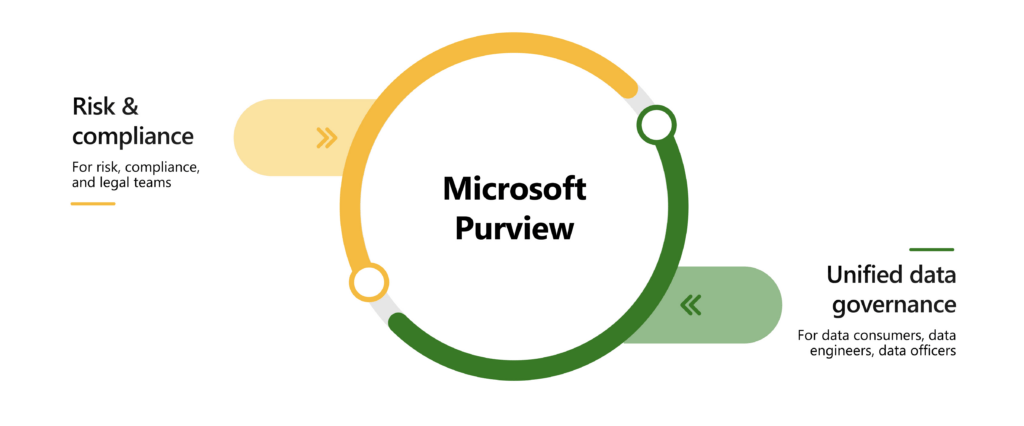
Across hybrid and multi-cloud contexts, any data-protection solution must handle the four discussed areas: unified discovery and protection, protection against data exfiltration, control of unstructured data, and a Zero Trust basis. Zero Trust is a basic architectural idea underlying both Microsoft 365 and Microsoft Azure. And with Microsoft Purview’s complete, integrated solutions for information protection, data governance, risk management, and compliance, you can move forward without fear.
Microsoft Purview’s data governance portal helps manage your entire data landscape. Microsoft Priva identifies data-privacy risks and automates mitigation. Microsoft Defender for Cloud Apps blocks attacks against your apps using automated identity governance. To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.